Save Save iso-27001-compliance-checklist.xls For Later. 86% (29) 86% found this document useful (29 votes). ISO Compliance audit Checklist. ISMS Risk Assessment Manual v1.4. ISO 27001 Internal Audit Checklist. Are you looking for this GDPR Appendix ISO 27001 Internal Audit Checklist? The EU General Data Protection Regulation (GDPR) is the most important change in data privacy regulation in 20 years. ISO 27001; 2013 transition checklist ISO 27001: 2013 – requirements Comments and evidence 0 Introduction 0.1 General There are some textural changes for example the new standard are. If you are planning your ISO 27001 or ISO 22301 internal audit for the first time, you are probably puzzled by the complexity of the standard and what you should check out during the audit. So, you’re probably looking for some kind of a checklist to help you with this task. Here’s the bad news: there is no universal checklist.
- Iso 27001 Checklist Xls
- Iso 27001 Compliance Checklist Xls
- Iso 27001 Internal Audit Checklist
- Iso Iec 27001 Audit Checklist
Time to sharpen up your information security management system? Thinking of using ISO as a framework? Richard Green, founder of Kingsford Consultancy Services, recommends getting to grips.
If you are planning your ISO 27001 or ISO 22301 internal audit for the first time, you are probably puzzled by the complexity of the standard and what you should check out during the audit. So, you’re probably looking for some kind of a checklist to help you with this task. Here’s the bad news: there is no universal checklist that could fit your company needs perfectly, because every company is very different; but the good news is: you can develop such a customized checklist rather easily.
The steps in the internal audit
Let’s see which steps you need to take to create a checklist, and where they are used. By the way, these steps are applicable for internal audit of any management standard, e.g. ISO 9001, ISO 14001, etc.:
- Document review. In this step you have to read all the documentation of your Information Security Management System or Business Continuity Management System (or part of the ISMS/BCMS you are about to audit) in order to: (1) become acquainted with the processes in the ISMS, and (2) to find out if there are nonconformities in the documentation with regard to ISO 27001 or ISO 22301.
- Creating the checklist. Basically, you make a checklist in parallel to Document review – you read about the specific requirements written in the documentation (policies, procedures and plans), and write them down so that you can check them during the main audit. For instance, if the Backup policy requires the backup to be made every 6 hours, then you have to note this in your checklist, to remember later on to check if this was really done.
- Planning the main audit. Since there will be many things you need to check out, you should plan which departments and/or locations to visit and when – and your checklist will give you an idea on where to focus the most.
- Performing the main audit. The main audit, as opposed to document review, is very practical – you have to walk around the company and talk to employees, check the computers and other equipment, observe physical security, etc. A checklist is crucial in this process – if you have nothing to rely on, you can be certain that you will forget to check many important things; also, you need to take detailed notes on what you find.
- Reporting. Once you finish your main audit, you have to summarize all the nonconformities you found, and write an Internal audit report – of course, without the checklist and the detailed notes you won’t be able to write a precise report. Based on this report, you or someone else will have to open corrective actions according to the Corrective action procedure.
- Follow-up. In most cases, the internal auditor will be the one to check whether all the corrective actions raised during the internal audit are closed – again, your checklist and notes can be very useful here to remind you of the reasons why you raised a nonconformity in the first place. Only after the nonconformities are closed is the internal auditor’s job finished.
Making your checklist usable for beginners
So, developing your checklist will depend primarily on the specific requirements in your policies and procedures.
But if you are new in this ISO world, you might also add to your checklist some basic requirements of ISO 27001 or ISO 22301 so that you feel more comfortable when you start with your first audit. First of all, you have to get the standard itself; then, the technique is rather simple – you have to read the standard clause by clause and write the notes in your checklist on what to look for.
By the way, the standards are rather difficult to read – therefore, it would be most helpful if you could attend some kind of training, because this way you will learn about the standard in a most effective way. (Click here to see a list of ISO 27001 and ISO 22301 webinars.)
What to include in your checklist
Iso 27001 Checklist Xls
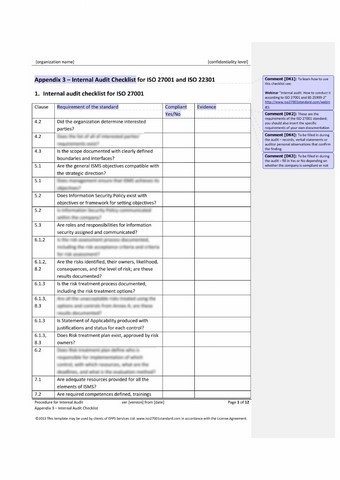
Normally, the checklist for internal audit would contain 4 columns:
- Reference – e.g. clause number of the standard, or section number of a policy, etc.
- What to look for – this is where you write what it is you would be looking for during the main audit – whom to speak to, which questions to ask, which records to look for, which facilities to visit, which equipment to check, etc.
- Compliance – this column you fill in during the main audit, and this is where you conclude whether the company has complied with the requirement. In most cases this will be Yes or No, but sometimes it might be Not applicable.
- Findings – this is the column where you write down what you have found during the main audit – names of persons you spoke to, quotes of what they said, IDs and content of records you examined, description of facilities you visited, observations about the equipment you checked, etc.
Don’t be afraid
So, performing the internal audit is not that difficult – it is rather straightforward: you need to follow what is required in the standard and what is required in the ISMS/BCMS documentation, and find out whether the employees are complying with those rules.
If you have prepared your internal audit checklist properly, your task will certainly be a lot easier.
Learn how to perform an internal audit in this freeISO 27001 Internal Auditor Online Course.
If you enjoyed this article, subscribe for updates
Improve your knowledge with our free resources on ISO 27001/ISO 22301 standards.
You may unsubscribe at any time.
For more information on what personal data we collect, why we need it, what we do with it, how long we keep it, and what are your rights, see this Privacy Notice.
Multipart article
We’ve compiled the most useful free ISO 27001 information security standard checklists and templates, including templates for IT, HR, data centers, and surveillance, as well as details for how to fill in these templates.
Included on this page, you'll find an ISO 27001 checklist and an ISO 27001 risk assessment template, as well as an up-to-date ISO 27001 checklist for ISO 27001 compliance.
ISO 27001 Checklist
Use this simple ISO 27001 checklist to ensure that you implement your information security management systems (ISMS) smoothly, from initial planning to the certification audit. This 14-step checklist provides you with a list of all stages of ISO 27001 execution, so you can account for every component you need to attain ISO 27001 certification. This reusable checklist is available in Word as an individual ISO 270010-compliance template and as a Google Docs template that you can easily save to your Google Drive account and share with others.
Download ISO 27001 Checklist
Excel | Word | PDF
ISO 27001 Risk Assessment Template
This ISO 27001 risk assessment template provides everything you need to determine any vulnerabilities in your information security system (ISS), so you are fully prepared to implement ISO 27001. The details of this spreadsheet template allow you to track and view — at a glance — threats to the integrity of your information assets and to address them before they become liabilities.
This simple template provides columns to detail asset name and number, confidentiality impact, risk details and rating, control details, and status. Use it as you seek ISO 27001 compliance certification.
Download ISO 27001 Risk Assessment Template - Excel
For more on ISMS, see “Everything You Need to Know about Information Security Management Systems.”
ISO 27001 Controls Checklist
Track the overall implementation and progress of your ISO 27001 ISMS controls with this easily fillable ISO 27001 controls checklist template. The template includes an ISO 27001 clause column and allows you to track every component of successful ISO 27001 implementation.
Additionally, enter details pertaining to mandatory requirements for your ISMS, their implementation status, notes on each requirement’s status, and details on next steps. Use the status dropdown lists to track the implementation status of each requirement as you move toward full ISO 27001 compliance.
Download ISO 27001 Controls Checklist
Excel | Word | Smartsheet
ISO 27001-2013 Auditor Checklist
This ISO 27001-2013 auditor checklist provides an easily scannable view of your organization’s compliance with ISO 27001-2013. Columns include control-item numbers (based on ISO 27001 clause numbering), a description of the control item, your compliance status, references related to the control item, and issues related to reaching full ISO 27001 compliance and certification.
Whether you need to perform a preliminary internal audit or prepare for an external audit and ISO 27001 certification, this easy-to-fill checklist helps ensure that you identify potential issues that must be addressed in order to achieve ISO 27001 compliance.
Download ISO 27001-2013 Auditor Checklist
Excel | Word
ISO 27001 Compliance Checklist
This single-source ISO 27001 compliance checklist is the perfect tool for you to address the 14 required compliance sections of the ISO 27001 information security standard.
Keep all collaborators on your compliance project team in the loop with this easily shareable and editable checklist template, and track every single aspect of your ISMS controls. This pre-filled template provides standards and compliance-detail columns to list the particular ISO 27001 standard (e.g., A.5.1 - Management Direction for Information, A.5.1.1 - Policies for Information Security, etc.), as well as assessment and results columns to track progress on your way to ISO 27001 certification.
Iso 27001 Compliance Checklist Xls
Download ISO 27001 Compliance Checklist
Excel | Word
For more on data security, see “Data Security 101: Understanding the Crisis of Data Breaches, and Best Practices to Keep Your Organization's Data Secure.”
ISO 27001 Internal Audit Schedule Template
Use this internal audit schedule template to schedule and successfully manage the planning and implementation of your compliance with ISO 27001 audits, from information security policies through compliance stages. Whether your eventual external audit is for information technology (IT), human resources (HR), data centers, physical security, or surveillance, this internal audit template helps ensure accordance with ISO 27001 specifications.
This internal audit schedule provides columns where you can note the audit number, audit date, location, process, audit description, auditor and manager, so that you can divide all facets of your internal audits into smaller tasks. Easily assess at-risk ISO 27001 components, and address them proactively with this simple-to-use template.
Download ISO 27001 Internal Audit Schedule Template
Excel | Word

For more on internal audits, see “Network Security 101: Problems & Best Practices.”
ISO 27001 Sample Form Template
Keep tabs on progress toward ISO 27001 compliance with this easy-to-use ISO 27001 sample form template.
The template comes pre-filled with each ISO 27001 standard in a control-reference column, and you can overwrite sample data to specify control details and descriptions and track whether you’ve applied them. The “Reason(s) for Selection” column allows you to track the reason (e.g., “risk assessment”) for application of any particular ISO 27001 standard and to list associated assets.
You can save this ISO 27001 sample form template as an individual file — with customized entries — or as a template for application to other business units or departments that need ISO 27001 standardization.
Download ISO 27001 Sample Form Template - Excel
ISO 27001 Business Continuity Checklist
Designed with business continuity in mind, this comprehensive template allows you to list and track preventative measures and recovery plans to empower your organization to continue during an instance of disaster recovery.
This checklist is fully editable and includes a pre-filled requirement column with all 14 ISO 27001 standards, as well as checkboxes for their status (e.g., specified, in draft, and done) and a column for further notes. Use this simple checklist to track measures to protect your information assets in the event of any threats to your company’s operations.
Download ISO 27001 Business Continuity Checklist
Excel | Word | PowerPoint
ISO 27002 Information Security Guidelines Checklist
Use this ISO 27002 information security guidelines checklist to ensure that your ISMS security controls adhere to the ISO 27001 information security standard. ISO 27002 provides an overview list of best practices for implementing the ISO 27001 security standard.
This ISO 27002 information security guidelines checklist provides an overview of security controls that should be managed through your ISMS and helps ensure that your controls are organized and up-to-date.
Download ISO 27002 Information Security Guidelines Checklist
Excel | Word
The Importance of the IS0 27001 Information Security Standard
The only way for an organization to demonstrate complete credibility — and reliability — in regard to information security best practices and processes is to gain certification against the criteria specified in the ISO/IEC 27001 information security standard. The International Organization for Standardization (ISO) and International Electrotechnical Commission (IEC) 27001 standards offer specific requirements to ensure that data management is secure and the organization has defined an information security management system (ISMS). Additionally, it requires that management controls have been implemented, in order to confirm the security of proprietary data.
By following the guidelines of the ISO 27001 information security standard, organizations can be certified by a Certified Information Systems Security Professional (CISSP), as an industry standard, to assure customers and clients of the organization’s dedication to comprehensive and effective data security standards.
In order to adhere to the ISO 27001 information security standards, you need the right tools to ensure that all 14 steps of the ISO 27001 implementation cycle run smoothly — from establishing information security policies (step 5) to full compliance (step 18).
Whether your organization is looking for an ISMS for information technology (IT), human resources (HR), data centers, physical security, or surveillance — and regardless of whether your organization is seeking ISO 27001 certification — adherence to the ISO 27001 standards provides you with the following five benefits:
- Industry-standard information security compliance
- An ISMS that defines your information security measures
- Client reassurance of data integrity and successive ROI
- A decrease in costs of potential data compromises
- A business continuity plan in light of disaster recovery
ISO 27001 and ISO 22301 work together to prevent and mitigate potential problems, especially when it comes to business continuity. To learn more, visit, 'ISO 22301 Business Continuity Simplified: Fortify Your Business Against Disruption.'
Up-to-Date ISO 27001 Checklist
An ISO 27001 checklist is crucial to a successful ISMS implementation, as it allows you to define, plan, and track the progress of the implementation of management controls for sensitive data. In short, an ISO 27001 checklist allows you to leverage the information security standards defined by the ISO/IEC 27000 series’ best practice recommendations for information security.
An ISO 27001-specific checklist enables you to follow the ISO 27001 specification’s numbering system to address all information security controls required for business continuity and an audit. It ensures that the implementation of your ISMS goes smoothly — from initial planning to a potential certification audit.
An ISO 27001 checklist provides you with a list of all components of ISO 27001 implementation, so that every aspect of your ISMS is accounted for. An ISO 27001 checklist begins with control number 5 (the previous controls having to do with the scope of your ISMS) and includes the following 14 specific-numbered controls and their subsets:
Iso 27001 Internal Audit Checklist
Information Security Policies:
Management direction for information security
Organization of Information Security:
Internal organization
Mobile devices and teleworking
Human Resources Security:
Prior to employment
During employment
Termination and change of employment
Asset Management:
Responsibilities for assets
Information classification
Media handling
Access Control:
Responsibilities for assets, user responsibilities, and system application access control
Cryptography:
Cryptographic controls
Physical and environmental security:
Secure areas
Equipment
Operations Security:
Operational procedures and responsibilities
Protection from malware
Backup
Logging and monitoring
Control of operational software
Technical vulnerability information systems audit considerations
Communications Security:
Network security management
Information transfer
System Acquisition, Development, and Maintenance:
Security requirements of information systems
Security in development and support processes
Supplier Relationships
Information Security Incident Management:
Information security management
Information Security Aspects of Business Continuity Management
Information security continuity
Redundancies
Business Continuity Management:
Compliance with legal and contractual requirements
Independent review of information security
Improve ISO 27001 Implementation with Smartsheet
To get the most out of your ISO 27001 implementation efforts — and meet compliance guidelines — you’ll need a tool that allows you to plan, track, and manage every aspect of ISO 27001 implementation in real time. One such tool is Smartsheet, an enterprise work execution platform that fundamentally changes the way teams, leaders, and businesses get work done. Over 80,000 brands and millions of information workers trust Smartsheet as the best way to plan, capture, manage, automate, and report on work.
You can build automated business processes without a single line of code, complex formulas, or help from IT. Achieve faster progress by creating automated approval requests and automated update requests that are triggered based on preset rules. Use Smartsheet to automate and streamline the following processes: time card tracking, sales discounts, procurement, HR hiring, content, and more. Plus, Smartsheet integrates with the tools you already use to seamlessly connect your efforts across applications.
Discover why over 80,000 brands trust Smartsheet to get work done.
Smartsheet is now certified to three industry-leading information Security and Data Privacy frameworks — ISO 27001, ISO 27018, and ISO 27701. For more information about the enterprise-level security and data privacy standards that Smartsheet upholds, visit our Trust Center.
Iso Iec 27001 Audit Checklist
Boost effectiveness and achieve more by building powerful, automated business processes in Smartsheet.
